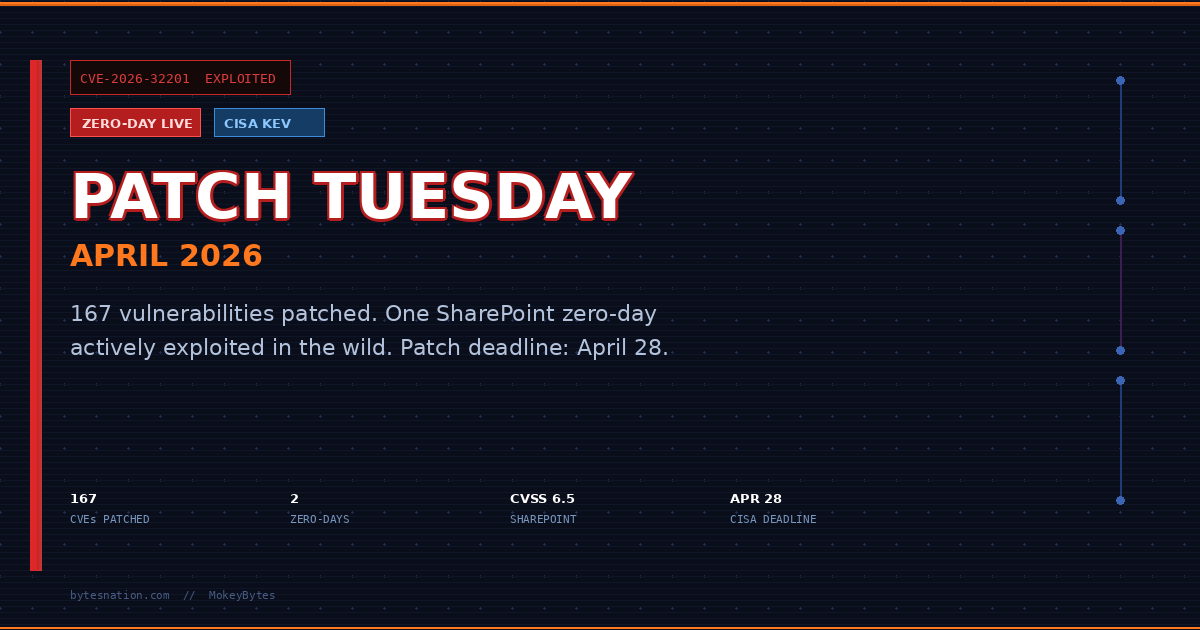
Network Firewalls vs. Web Application Firewalls: What Each One Actually Defends
Network Firewalls vs. Web Application Firewalls: What Each One Actually Defends
Both devices are called firewalls. Both block traffic. That is where the similarity ends.
Network firewalls and Web Application Firewalls (WAFs) operate at different layers of the OSIA seven-layer framework that describes how data travels from an application on one device to an application on another device across a network. Read more → model, inspect different things, and fail against different attack types. Running one without the other leaves real gaps. Understanding the difference is not an academic exercise; it is the foundation of any layered security architecture.
The Core Distinction: Which Layer They Inspect
A network firewallA security device or software that monitors and controls incoming and outgoing network traffic based on predefined rules. Read more → works at Layers 3 and 4 of the OSI model, the Network and Transport layers. It sees IPA unique numerical label assigned to every device on a network, used to identify it and route traffic to the correct destination. Read more → addresses, ports, and protocols. It makes decisions based on those values: allow TCPA transport protocol that guarantees reliable, ordered delivery of data between two devices by establishing a connection before sending. Read more → from this IP to portA numbered endpoint on a device that identifies a specific application or service, allowing multiple network services to run on the same IP address. Read more → 443, block everything else from this subnet, deny UDPA lightweight transport protocol that sends data without establishing a connection first, prioritizing speed over guaranteed delivery. Read more → except from these sources.
A WAFA firewall that operates at the application layer (Layer 7) to protect web applications from attacks like SQL injection and cross-site scripting. Read more → works at Layer 7, the Application layer. It sees the actual content of HTTP and HTTPS requests: the URL path, query parameters, headers, cookies, and request body. It makes decisions based on what is inside the traffic, not just where it came from.
That distinction determines everything about what each device can and cannot protect against.
What Network Firewalls Do Well
Network firewalls are the perimeter. They answer the question: should this connection be allowed to exist at all?
A well-configured network firewall blocks inbound connections to ports you are not running services on. It prevents direct access to your database server from the public internet. It enforces network segmentation so a compromised web server cannot directly reach your internal DNSThe system that translates human-readable domain names into IP addresses so devices can find each other on a network. Read more → or Active Directory. It rate-limits or drops flood traffic before it saturates upstream links.
Stateful packet inspection lets a modern firewall track connection state, not just individual packets. It can allow an outbound TCP connection to be initiated from inside your network and permit the inbound response traffic without opening a broad inbound rule. This is the difference between a stateless packet filter and an actual firewall.
Intrusion prevention capabilities in next-generation firewalls (NGFWs) extend this further. They can detect and block known exploit patterns, command-and-control callbacks, and malicious DNS lookups using signature-based detection at the network layer.
What a network firewall cannot do: it cannot read the contents of an HTTP request that arrives on port 443. If the connection is allowed, the firewall lets it through. What happens inside that HTTP request is invisible to it.
What Web Application Firewalls Do Well
A WAF defends the application from traffic that already has permission to connect.
SQL injection is the canonical example. An attacker sends a POST request to your login form with a payload like ' OR 1=1 -- in the username field. The connection came from a legitimate IP, over port 443, using HTTPS. A network firewall sees nothing wrong. The WAF reads the request body, matches the payload against SQL injection signatures, and blocks the request before it reaches your application code.
The same principle applies to cross-site scripting (XSS), where an attacker tries to inject <script> tags into a form field that will later be rendered in another user’s browser. Or path traversal attacks, where a request to /api/files?path=../../etc/passwd is trying to read your server’s password file. Or HTTP request smuggling, where malformed headers try to desynchronize a proxy and backend server to sneak unauthorized requests through.
All of these attacks arrive on allowed ports from non-blocked IPs. The network firewall has no mechanism to detect them. The WAF exists specifically to inspect the HTTP layer and block them.
WAFs also handle rate limiting at the application layer. Not just “this IP is sending too many TCP connections” but “this IP has submitted 50 login attempts in 30 seconds” or “this client is scraping every product page on your site at 200 requests per minute.” Application-layer rate limiting lets you enforce much more meaningful thresholds than connection-level throttling.
Where Each One Fails
Network firewall blind spots:
Encrypted HTTPS traffic is the biggest gap. A network firewall sees that encrypted data is flowing over port 443, but it cannot inspect the contents without performing TLS termination, which introduces latency, certificates, and complexity that most organizations skip. Everything inside TLS is opaque to a standard network firewall.
Zero-day application exploits that do not match known signatures will pass through most network firewall inspection engines. A novel SQL injection technique or a new deserialization gadget chain in your Java application is not a network-layer event.
Authorized users abusing their access. If an authenticated user is exfiltrating data through a legitimate API endpoint, the network firewall sees legitimate traffic from an authorized source.
WAF blind spots:
Network-layer attacks are completely out of scope. A volumetric DDoS flood, a port scan, an attempt to connect directly to a database port, ARP spoofing on the local network. The WAF only sees HTTP/HTTPS. Everything else is invisible to it.
Encrypted bypasses. If a WAF is deployed in a pass-through mode without TLS termination, encrypted traffic is as opaque to it as it is to the network firewall. Many WAFs require you to terminate TLS at the WAF to inspect traffic properly, which means your WAF holds your SSL certificates.
Business logic flaws. A WAF cannot understand that your application should only allow a user to purchase one unit of a limited item, or that a password reset token should expire after one use, or that an account should lock after five failed login attempts if you have not implemented that logic in your app. WAFs block known attack patterns; they do not understand your application’s intent.
OSI Layer Reference
| Device | OSI Layers | Sees | Cannot See |
|---|---|---|---|
| Network Firewall | 3-4 (Network, Transport) | IP, port, protocol, connection state | HTTP content, URLs, query params, cookies |
| WAF | 7 (Application) | HTTP/HTTPS content, headers, body, URLs | Non-HTTP traffic, IP-level attacks |
| NGFW with TLS inspection | 3-7 | Everything above, decrypted | Attacks that evade signatures |
Deployment Patterns
Edge network firewall, WAF in front of web tier:
The most common architecture. Network firewall at the perimeter handles all inbound traffic. Only ports 80 and 443 pass through to the DMZ. WAF sits in front of the web servers, terminates TLS, inspects HTTP, and forwards clean traffic. Network firewall also enforces east-west rules: the web tier cannot initiate connections to the database tier except on the application port.
Internet
|
[Network Firewall] ← blocks all non-80/443 inbound
|
[WAF / Load Balancer] ← terminates TLS, inspects HTTP
|
[Web Servers]
|
[Network Firewall] ← internal segmentation rule
|
[Database Servers]Cloud WAF with on-prem network firewall:
If you are running on AWS, GCP, or Azure, you likely have cloud-native WAF options (AWS WAF, Azure Application Gateway with WAF, Cloudflare WAF). These sit in front of your cloud-hosted application and handle HTTP inspection. Your VPC security groups or cloud firewall rules handle network-layer access control. The two layers stack without requiring you to run your own WAF appliance.
Reverse proxy as WAF:
NGINX and HAProxy can perform basic WAF functions via ModSecurity or similar modules. If you do not have budget for a dedicated WAF appliance, a reverse proxy configured with the OWASP Core Rule Set (CRS) provides a meaningful baseline. It is not a full commercial WAF, but it will catch the most common automated attacks.
When You Need Both
The answer to “do I need both?” is almost always yes if you are running any web-facing application.
The network firewall protects your infrastructure. It enforces the principle that only the services you intend to expose are reachable from the internet. It prevents lateral movement if a host is compromised. It gives you the ability to block entire IP ranges, countries, or ASNs at scale.
The WAF protects your application. It handles the attack surface that exists within legitimate HTTP traffic, which is the attack surface that matters most for anything a user can reach through a browser.
Neither replaces the other. A network firewall with no WAF leaves your application unprotected against SQL injection, XSS, and every other Layer 7 attack. A WAF with no network firewall leaves your infrastructure directly exposed: a misconfigured port, an unintended service, a debug endpoint that should never have been reachable from the internet.
Run both. Put the network firewall at the edge. Put the WAF in front of the application tier. Configure rules on both. Review logs on both.
Virtual Firewalls in Cloud Environments
Cloud environments blur the hardware distinction but not the functional one. Virtual firewalls and security groups handle Layer 3 and 4 access control for your cloud network: which VMs can talk to which, which ports are open, what traffic is allowed in from the internet. Cloud WAFs handle Layer 7 inspection for web-facing services.
| Aspect | WAF | Virtual Firewall / Security Group |
|---|---|---|
| OSI Layer | 7 (Application) | 3-4 (Network, Transport) |
| Protection Target | Web servers, APIs, applications | Networks, VMs, containers, cloud resources |
| Attack Types | XSS, SQLi, path traversal, API abuse | Port scans, unauthorized connections, DDoS at L3/4 |
| Traffic Inspected | HTTP/HTTPS content | Any protocol (TCP, UDP, ICMP) |
| Typical Deployment | In front of application tier | VPC/network perimeter and internal segments |
The cloud provider gives you both primitives. Use both. Security groups are not optional because you have a WAF. A WAF is not optional because you have security groups.
The Practical Summary
If someone compromises a router on your network, a network firewall controls whether that router can reach your database. A WAF has nothing to say about it. If someone submits a SQL injection payload through your contact form, a WAF catches it. A network firewall has nothing to say about it.
Different threats. Different defenses. Neither is complete without the other.